Google’s Chrome and Mozilla’s Firefox are both separately advocating the move to a new encrypted internet protocol called DNS over HTTPS aimed at improving cybersecurity on the web.
But internet service providers (ISPs) are up in arms, and Congress is dubious of the motivation, at least in Google’s case.
What’s going on and what does it mean for ISPs?
The internet’s (insecure) phonebook
Taking a step back, an internet protocol is an agreed-upon set of rules that allows data to be transferred from one computer to another over the internet, hence the term “IP address.”
One of the oldest and most widely used protocols on the internet is called DNS, which stands for domain name system, and is how a human-readable domain is entered into a browser and connected to a numerical IP address. Think of it is as the internet’s phone book.
Unencrypted DNS has been in use for decades and it’s an entrenched part of how the internet functions, but there’s a problem: “It’s wildly insecure,” said David Holmes, a senior analyst at Forrester focused on cybersecurity.
The DNS protocol is particularly vulnerable to distributed denial of service attacks, for example. Among other things, bad actors have also been known to take advantage of DNS to typosquat, which is the practice of registering URLs for common misspellings of popular domains usually for the purpose of redirecting traffic to phishing sites.
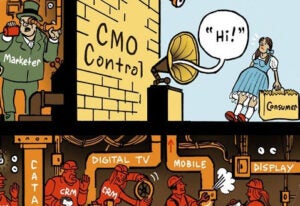
And because DNS queries are rarely encrypted, ISPs can track the browsing habits of their subscribers, including which sites people visit and how long they spend there.
And ISPs can monetize this information primarily by selling it to advertisers looking to serve personalized ads.
“ISPs also know your IP address, of course, because they’re the one that issued it to you,” said Gregg Siegfried, a research director on Gartner’s cloud and IT operations team.
The move to DNS over HTTPS
What Google and Mozilla are proposing is to start encrypting DNS requests, aka, DNS over HTTPS (also known as DoH), although their approaches are slightly different.
For Mozilla, DNS over HTTPS is the default in Firefox as of September and all requests are automatically routed through web infrastructure company Cloudflare, which supports the encrypted DNS protocol.
Chrome, which plans to start testing the encrypted protocol this month, is taking a less nuclear option by keeping the DNS provider as is and only upgrading to DNS over HTTPS if that provider offers it.
If there’s an error or some other issue with a DNS over HTTPS lookup, both Chrome and Firefox will fall back to regular DNS so as not to disrupt the user experience.
ISPs in an uproar
In theory, DNS over HTTPS will stop ISPs from knowing what sites someone is browsing.
ISPs are worried they’ll be cut off from their “traditional middleman position between the browser and the end DNS server,” said Hugo Loriot, US managing director of You & Mr Jones-owned data agency fifty-five.
Although Google’s DoH GitHub documentation makes no mention of ISPs or tracking, “depriving ISPs from data about what website subscribers are visiting has a lot to do with tracking,” Loriot said.
But ISPs are cloaking their displeasure with other complaints.
For example, ISPs are fearful that if they lose visibility into what people are querying on the internet, they won’t be able to filter or block problematic or objectionable sites, like pedophilia.
There are also antitrust concerns. According to The Wall Street Journal, a coalition of ISPs and telecom trade groups griped in a Sept. 19 letter to lawmakers that there could be a competition issue if Chrome and/or Android moves to DNS over HTTPS, because Google would then be able to leverage Chrome’s outsize market share to become the internet’s main DNS lookup provider and get even more access to user data across networks.
The Journal also reports that the House Judiciary Committee, which is running its own antitrust investigation into big tech platforms, sent a request to Google in mid-September for more information on how data is collected through the new protocol and whether it’ll be used for commercial purposes.
For its part, Google claims it has no intention to force users onto its own DNS encrypted servers, and that moving to DNS over HTTPS is a long overdue shoring up of DNS-related security flaws.
Reality check
It’s easy to raise a suspicious eyebrow when Google professes to have no ulterior motives behind its actions.
“Putting Firefox aside, a cynic would say that a move to DoH means Google is the only company who’s going to know about people’s surfing habits,” said Forrester’s Holmes.
But Google doesn’t actually need another source for that data – it already has access to all your browsing info through Chrome, Holmes said. The fear, then, is that Google would attempt to deny that data to other parties, like ISPs. “You could think of it as a competition issue at that point,” he said.
Yet, the move toward encryption is a positive thing, and that Google and Mozilla actually agree on something “appears to speak to the fact that this really is about privacy and protecting users,” Holmes said.
It’s also important to separate the policy from the mechanism, said Gartner’s Siegfried. “The more you encrypt the internet the better, and I think ISPs share that perspective,” he said. “What they don’t want is the policy, because there are so few DNS over HTTPS servers out there right now.”
Once the standards get more established and ISPs have their own DoH servers in place, “there will be less of an outcry,” Siegfried said.
But in terms of ISPs looking to monetize their data at all, the writing might be on the wall regardless of what policies Chrome or Firefox institute.
The Federal Trade Commission is starting to look into the privacy and data collection practices of advertising subsidiaries owned by broadband companies, such as Oath (now Verizon Media) and AppNexus.
It’s not a full-blown investigation, more of an early-stage fact-finding exercise – but it does speak to growing scrutiny of how ISPs collect, use and share data.